By all outward appearances, the emails seem to come from Craigslist in response to ads posted in Craigslist’s “Gigs” section for short term employment. The emails will generally express interest in whatever job the user has posted and include a protected Word or RTF document which recipients will assume are resumes.
If the recipient enters the password to unlock the document, they’ll then be presented with a screen that asks them to enable the content in the document. Unfortunately, this is the step that dooms the user. The file isn’t a resume at all, but merely a delivery vehicle.
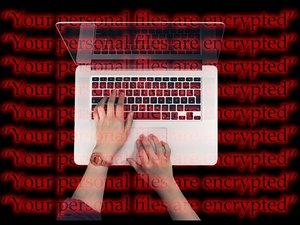
As soon as the content is enabled, the ransomware will be installed, the user’s files will be encrypted, and then will “helpfully” post a message explaining that the files have been encrypted, and explaining that to get access to them again, they’ll have to pay a $400 fee, which rises to $800 if the user waits longer than seven days to request the decryption key.
Unfortunately, there’s no known way to decrypt Sigma-encrypted files other than paying the ransom.
This is a new twist on a very old game. Even worse, it’s enjoying a relatively high success rate because people who post ads for short term employment on Craigslist expect to get responses from people they don’t know. They expect that those people will be sending resumes for review.
The “tell” is that when a potential employee sends you a resume, it’s almost certainly not going to be password protected. In this case, your best bet would be to reply to the sending and ask them to send you a non-protected resume if they’re genuinely interested in the job.
Used with permission from Article Aggregator