by Master User | Jun 15, 2016 | Blog
If you’re one of the millions of users with an Android phone, then you already know there are a couple of different ways you can find it if you happen to misplace it. You can use the built-in search feature, or the Device Manager app. As of now, Google has rolled out...

by Master User | Jun 14, 2016 | Blog
Have you been noticing “strange” search results when you’re surfing the web? Have your search results been taking longer than usual to appear? You may have been infected by a new, very clever bit of malware known as Redirector.Paco. There are actually two flavors of...
by Master User | Jun 13, 2016 | Blog
What percentage of total internet traffic would you estimate that bots (non-human visitors) account for? Twenty percent? Thirty percent? Unfortunately, according to data released by DeviceAtlas, a company that makes software to detect the kinds of devices web visitors...

by Master User | Jun 11, 2016 | Blog
If you haven’t yet heard of “KeySweeper,” you have a new threat to be on the lookout for. The KeySweeper device is built with off the shelf, Arduino components. These can be programmed for a variety of purposes, but the hacking community is using them as stealthy...

by Master User | Jun 10, 2016 | Blog
In recent months, Microsoft has made a number of very good, highly popular moves that have had its customers raving about its apparent change. This latest incident, however, isn’t one of those. Microsoft has been accused of resorting to malware-style tactics to try...
by Master User | Jun 9, 2016 | Blog
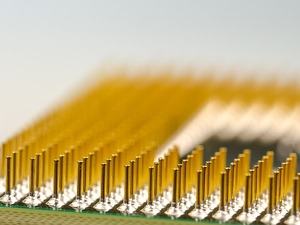
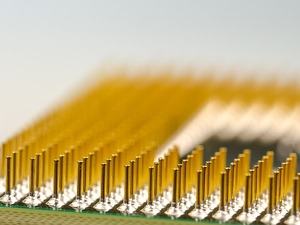
You’ve probably got either a dual- or quad-core computer sitting on your desk right now, but if you love bleeding edge technology, then you’re going to want to upgrade after reading this. Recently, at the Computex trade show in Taipei, intel unveiled its first ever...